The TechBeat: The Hidden Cost of AI: Why It’s Making Workers Smarter, but Organisations Dumber (1/3/2026)
How are you, hacker? 🪐Want to know what's trending right now?: The Techbeat by HackerNoon has got you covered with fresh content from our trending stories of the day! Set email preference here. ## The Hidden Cost of AI: Why It’s Making Workers Smarter, but Organisations Dumber  By @yuliiaharkusha [ 8 Min read ] AI boosts individual performance but weakens organisational thinking. Why smarter workers and faster tools can leave companies less intelligent than before. Read More.
By @yuliiaharkusha [ 8 Min read ] AI boosts individual performance but weakens organisational thinking. Why smarter workers and faster tools can leave companies less intelligent than before. Read More.
Why Verifiability Matters for Security: 12 Key Cloud Application Use Cases 
By @michaellewellen [ 3 Min read ] Verifiability is becoming essential for crypto, AI, and cloud apps. Learn why proving how systems run will shape the next gen of secure infrastructure. Read More.
Secury Wallet Unveils Next-Generation Multichain Crypto Wallet With Chat to Pay, Opens $SEC Presale 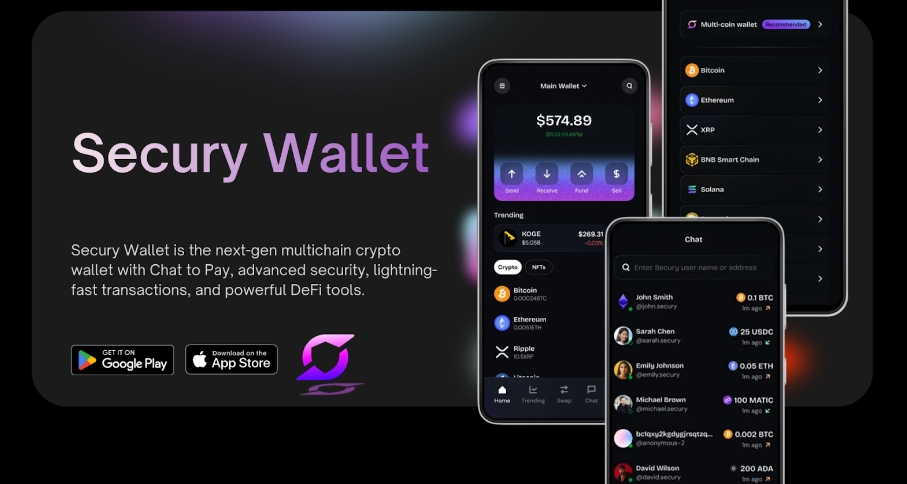
By @btcwire [ 2 Min read ] The project has opened the $SEC token presale, including early staking opportunities offering up to 100% APY during the presale phase. Chat to Pay is an instant Read More.
Should You Trust Your VPN Location? 
By @ipinfo [ 9 Min read ] IPinfo reveals how most VPNs misrepresent locations and why real IP geolocation requires active measurement, not claims. Read More.
A Developer's Guide to Building Next-Gen Smart Wallets With ERC-4337 — Part 2: Bundlers 
By @hacker39947670 [ 15 Min read ] Bundlers are the bridge between account abstraction and the execution layer. Read More.
How to Build an n8n Automation to Read Kibana Logs and Analyze Them With an LLM 
By @indrivetech [ 6 Min read ] How we built an n8n automation that reads Kibana logs, analyzes them with an LLM, and returns human-readable incident summaries in Slack Read More.
Tech's Attempt To Conquer Hollywood 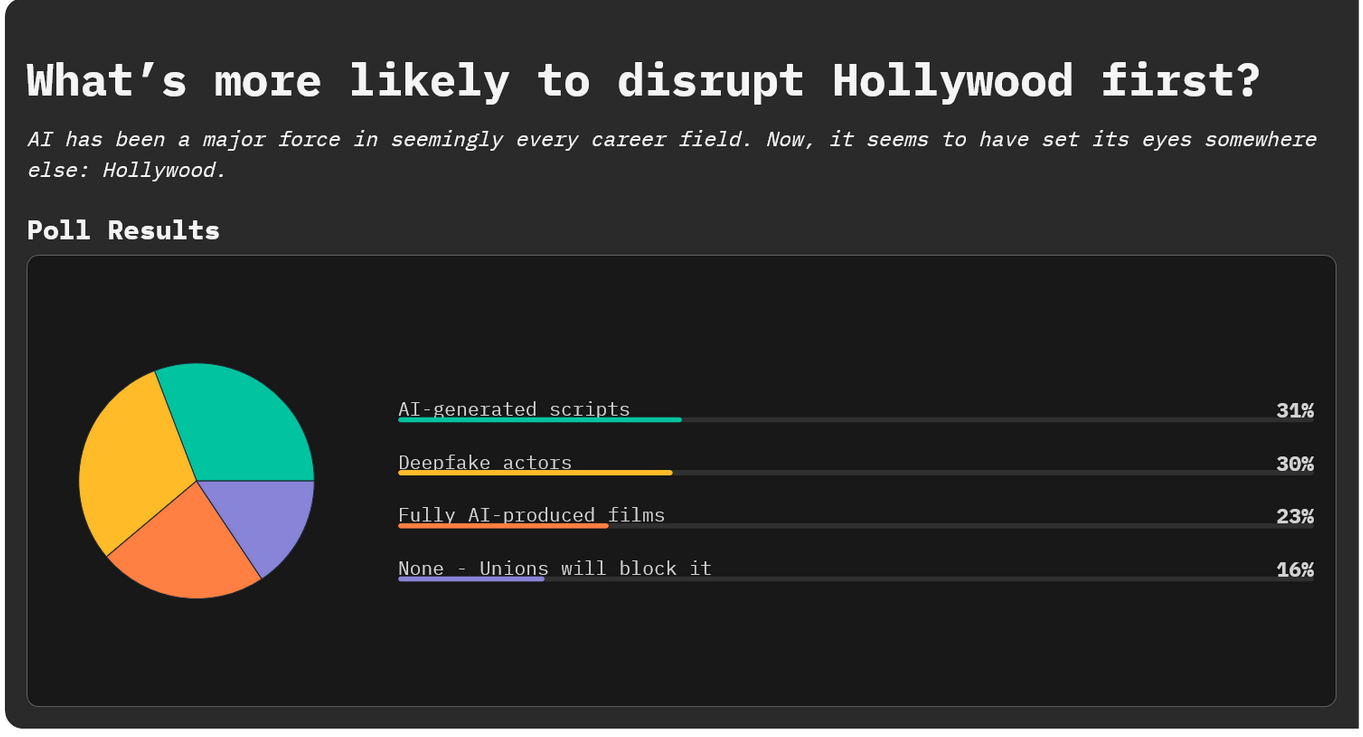
By @3techpolls [ 5 Min read ] AI has been a major force in seemingly every career field. Now, it seems to have set its eyes somewhere else: Hollywood. Read More.
Meet ScyllaDB: HackerNoon Company of the Week 
By @companyoftheweek [ 4 Min read ] Meet ScyllaDB, the high-performance NoSQL database delivering predictable millisecond latencies for Discord and hundreds more. Read More.
AI - Should we Be Afraid? 3 Years Later 
By @djcampbell [ 6 Min read ] Is AI good or bad? We must decide. Read More.
Hiring Didn’t Fail - Evidence Did. 
By [@Dandilion Civilization](https://hackernoon.com/u/Dandilion Civilization) [ 5 Min read ] I didn’t break hiring. It broke the evidence. Why CVs and training signals no longer predict capability, and what HR should use instead in 2026 Read More.
Coding Rust With Claude Code and Codex 
By @tigranbs [ 10 Min read ] How Rust's strict compiler transforms AI coding tools into reliable pair programmers and why the language is uniquely positioned for the age of agentic coding Read More.
How Crypto Can Protect People from Currency Wars 
By @chris127 [ 8 Min read ] When we think of war, we imagine soldiers, weapons, and physical destruction. But there's another type of war that affects millions of people worldwide… Read More.
The 10 Most Interesting C# Bugs We Found in Open Source in 2025 
By @akiradoko [ 15 Min read ] If you'd like to check whether your project has similar issues, now's the time to use a static analyzer. Read More.
10 AI Marketing Strategies for Startups in 2026 
By @khamisihamisi [ 4 Min read ] Over 90% of companies are either using or exploring the use of AI. How is your business using AI? Read More.
Best Amazon Scraper APIs for 2025: Top Picks Compared 
By @oxylabs [ 9 Min read ] Compare the best Amazon Scraper APIs for 2025, analyzing speed, pricing, reliability, and features for scalable eCommerce data extraction. Read More.
Slop Isn’t the Problem. It’s the Symptom. 
By @normbond [ 3 Min read ] When teams move fast without shared meaning, quality dissolves quietly. Why slop is a symptom of interpretation lag, not a technology failure. Read More.
The Architecture of Collaboration: A Practical Framework for Human-AI Interaction 
By @theakashjindal [ 7 Min read ] AI focus shifts from automation to augmentation ("Collaborative Intelligence"), pairing AI speed with human judgment to boost productivity. Read More.
you’re not burned out, you’ve got context obesity 
By @raysvitla [ 9 Min read ] you’re not burned out – you’ve got context obesity. why ai tools and “100 prompts” add chaos, and how to rebuild your context stack. Read More.
The Seven Pillars of a Production-Grade Agent Architecture 
By @denisp [ 12 Min read ] An AI agent without memory is just a script. An agent without guardrails is a liability. The 7 critical pillars of building production-grade Agentic AI. Read More.
The HackerNoon Newsletter: The Power and Peril of Anthropomorphized AI (12/27/2025) 
By @noonification [ 2 Min read ] 12/27/2025: Top 5 stories on the HackerNoon homepage! Read More. 🧑💻 What happened in your world this week? It's been said that writing can help consolidate technical knowledge, establish credibility, and contribute to emerging community standards. Feeling stuck? We got you covered ⬇️⬇️⬇️ ANSWER THESE GREATEST INTERVIEW QUESTIONS OF ALL TIME We hope you enjoy this worth of free reading material. Feel free to forward this email to a nerdy friend who'll love you for it. See you on Planet Internet! With love, The HackerNoon Team ✌️ 

You May Also Like

U.S. Moves Grip on Crypto Regulation Intensifies

The Role of Blockchain in Building Safer Web3 Gaming Ecosystems
- Immutable Ownership of Assets Blockchain records can be manipulated by anyone. If a player owns a sword, skin, or plot of land as an NFT, it is verifiably in their ownership, and it cannot be altered or deleted by the developer or even hacked. This has created a proven track record of ownership, providing control back to the players, unlike any centralised gaming platform where assets can be revoked.
- Decentralized Infrastructure Blockchain networks also have a distributed architecture where game data is stored in a worldwide network of nodes, making them much less susceptible to centralised points of failure and attacks. This decentralised approach makes it exponentially more difficult to hijack systems or even shut off the game’s economy.
- Secure Transactions with Cryptography Whether a player buys an NFT or trades their in-game tokens for other items or tokens, the transactions are enforced by cryptographic algorithms, ensuring secure, verifiable, and irreversible transactions and eliminating the risks of double-spending or fraudulent trades.
- Smart Contract Automation Smart contracts automate the enforcement of game rules and players’ economic exchanges for the developer, eliminating the need for intermediaries or middlemen, and trust for the developer. For example, if a player completes a quest that promises a reward, the smart contract will execute and distribute what was promised.
- Anti-Cheating and Fair Gameplay The naturally transparent nature of blockchain makes it extremely simple for anyone to examine a specific instance of gameplay and verify the economic outcomes from that play. Furthermore, multi-player games that enforce smart contracts on things like loot sharing or win sharing can automate and measure trustlessness and avoid cheating, manipulations, and fraud by developers.
- Cross-Platform Security Many Web3 games feature asset interoperability across platforms. This interoperability is made viable by blockchain, which guarantees ownership is maintained whenever assets transition from one game or marketplace to another, thereby offering protection to players who rely on transfers for security against fraud. Key Security Dangers in Web3 Gaming Although blockchain provides sound first principles of security, the Web3 gaming ecosystem is susceptible to threats. Some of the most serious threats include: